Difference Between Active and Passive Attacks in Tabular Form
Contents
- The major difference between active and passive attacks is that inactive attacks the attacker intercepts the connection and modifies the information.
- X.800 is a service provided by a protocol layer of communicating open systems, to ensure enough security of the system/ organization or the data transfer.
- RFC 2828 defines security service as a communication service provided by a system to given protection to the system resources.
- The X.800 and RFC2828 classify the security as:
- Active Attacks
- Passive Attacks

Comparison Chart
| Active Attack | Passive Attack |
|---|---|
| Attacker needs to have physical control of the media or network. | Attacker merely needs to observe the communication in the media or network. |
| It can be easily detected. | It cannot be easily detected. |
| It affects the system. | It does not affect the system. |
| It involves a modification of data. | It involves the monitoring of data. |
| Types of active attacks are Masquerade, session replay, denial of service, distributed denial of service. | Types of passive attacks are the Release of a message, traffic analysis. |
| It does not check for loopholes or vulnerabilities. | It scans the ports and network in the search of loopholes and vulnerabilities. |
| It is difficult to prevent network from active attack. | Passive attacks can be prevented. |
Active Attacks
- Active attacks involve modification of a data stream or creation of a false stream of messages.
- The attacker’s aim in such type of attack is to corrupt or destroy the data as well as the network itself.
-
- Active Attacks
- Active attacks are divided into four categories :
- Masquerade
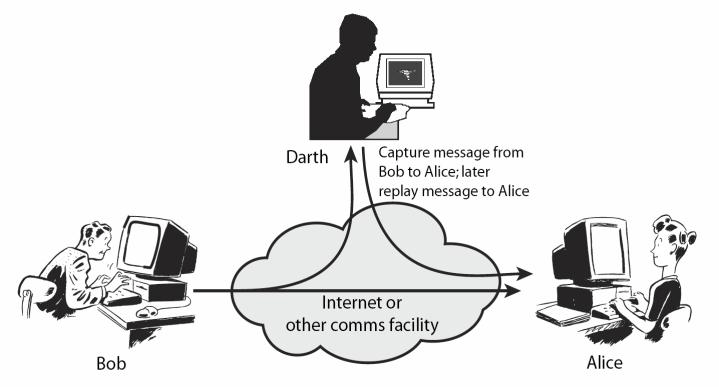
- Replay Attack
- Modification of Messages
- Denial of Service
Passive Attacks
- A passive attack makes an attempt to collect information from the system but does not modify or alter the system data or resources. Eavesdropping or monitoring of information is an example of passive attacks.
- The two types of passive attacks are:
- Release of message contents
- Traffic analysis
