Difference Between Symmetric and Asymmetric Encryption
Contents
Difference Between Symmetric and Asymmetric Key Cryptography.
- There are two types of Cryptography Symmetric Key Cryptography and Asymmetric Key Cryptography.
- The fundamental difference that distinguishes symmetric and asymmetric encryption is that symmetric encryption allows encryption and decryption of the message with the same key. On the other hand, asymmetric encryption uses the public key for the encryption, and a private key is used for decryption.
Comparison Chart
| Symmetric Encryption | Asymmetric Encryption |
|---|---|
| Symmetric Encryption single or the same key is used for encryption and decryption. | In asymmetric key cryptography, two keys are used, one is for encryption, and the other is for decryption. |
| Symmetric key cryptography is also called secret-key cryptography or private key cryptography. | Asymmetric key cryptography is also called public-key cryptography or a conventional cryptographic system. |
| Mathematically it is represented as P = D (K, E(P)). Where K is the encryption and decryption key. P= plain text, D= Decryption , E(P) = Encryption of plain text |
Mathematically it represented as P = D(Kd, E (Ke,P)), Where Ke and Kd are encryption and decryption key. D=Decryption E(Ke, P) = Encryption of plain text using private key Ke. |
| The symmetric key is faster than asymmetric key cryptography. | The asymmetric key is slower than symmetric key cryptography. Because of two different key used |
| For encryption of large message asymmetric key cryptography still play an important role. | Asymmetric key cryptography plain text and cipher text treated as integer numbers. |
| Symmetric key cryptography utilizes fewer resources as compared to asymmetric key cryptography. | Asymmetric key cryptography utilizes more resources as compared to symmetric key cryptography. |
| For Example AES, DES, and BLOWFISH | For Example RSA, Diffie Hellman Key exchange algorithm. |
Symmetric Encryption
- Symmetric cipher models also called secret-key cryptography or symmetric key cryptography.
- In symmetric-key cryptography, a single key is used for encryption as well as decryption.
- As shown in the image sender encrypts plain text using a shared secret key and the resultant ciphertext is transmitted through a communication medium such as the Internet, at the receiver side, the ciphertext is decrypted using the same decryption key to obtain the original plain text.
- Note that the encryption and decryption process uses a well-known symmetric key algorithm called as Data Encryption Standard (DES).
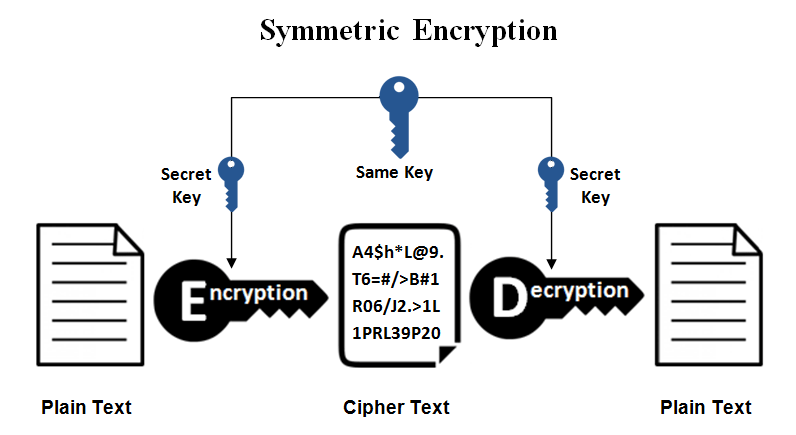
- Encryption of plain text, D (K, E(P)) = Decryption of Plain text using shared key K.
- For Example, Stream and block cipher, Data Encryption Standard (DES), Advanced Encryption Standard (AES), and BLOWFISH.
- Here the possibility is that if an attacker/opponent got cipher text ?? he/she might apply different permutations and combinations to decrypt and obtain the original plain text. Here the main aim of cryptography comes into the picture. Always sender has to think about applying different encoding techniques on the plain text messages and convert them into ciphertext messages so that the attacker cannot read the actual plain text easily.
Advantages of Symmetric Encryption
- A Symmetric key is faster than asymmetric key cryptography
- Because of single key data cannot decrypt easily at receiver side even if it is intercepted by the attacker
- As the same key is used for encryption and decryption, a receiver must have the senders otherwise he cannot decrypt (without sender permission).
- The symmetric key achieves the authentication principle because it checks the receiver’s identity.
- DES and AES techniques are implemented using symmetric key cryptography.
- System resources are less utilized in symmetric key cryptography
Disadvantages of Symmetric Encryption
- Once the key is stolen while transmitting data between sender and receiver it is very easy to decrypt the message as the same key is used for encryption and decryption
- symmetric-key cryptography, a key is transmitted first and then a message is transferred to the receiver. If the attacker intercepts the communication between sender and receiver, then he can decrypt the message before it reaches to intended recipients
Asymmetric Encryption
- Asymmetric key cryptography is also called public-key cryptography.
- In asymmetric key cryptography, two keys are used, one for encryption and the other for decryption.
- As mentioned asymmetric key cryptography involves the use of two keys one is a public key that may know to everyone and can be used to encrypt messages and verify signatures. Another is a private key known only to the receiver of the message or verifier, used to decrypt messages, and sign (create) signatures.
- It is also called asymmetric key cryptography because one key is used for encryption only its corresponding key must be used for decryption. No other key can decrypt the message. The sender and receiver can encrypt messages using an encryption key (public) or verify signatures, he cannot decrypt messages or create signatures because he required a decryption key (private) which is known only to the receiver of the message. Public key cryptosystem /asymmetric key cryptography is shown in the image.
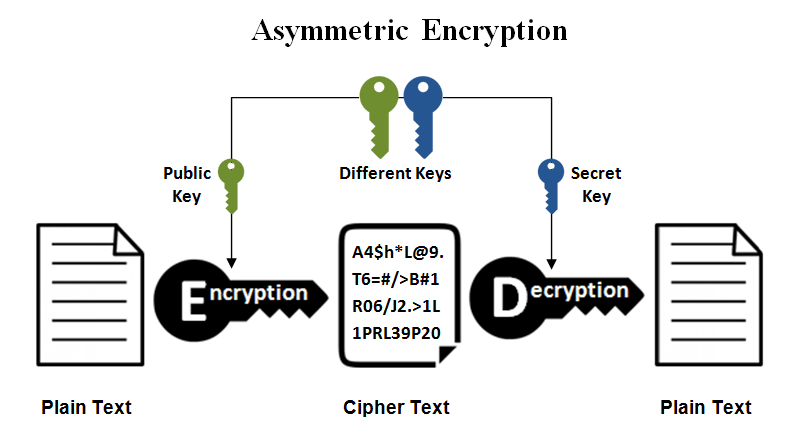
- Mathematically it is represented as P = D(Kd, E (Ke, P))
- For example, sender Ramesh wants to communicate with the receiver Suresh then they must have each one of these i.e. private key and public key then and then communication will be successful.
Advantages of Asymmetric Encryption
- In asymmetric key cryptography, a key cannot be distributed among sender and receiver as both have their own key, so there is no problem of key distribution while transmitting the data over the insecure channel.
- The main advantage of asymmetric key cryptography is that two separate keys are used for used encryption and decryption; even if the encryption key is stolen by an attacker he/ she cannot decrypt the message as the decryption key is only available with the receiver only.
- RSA algorithm and Diffie Hellman key exchange are implemented using asymmetric key cryptography.
- Easy to use for users and scalable does not require much administrative work.
Disadvantages of Asymmetric Encryption
- Because a different key used between sender and receiver requires more time to get the transmission done as compared to symmetric-key cryptography. (Slower that symmetric key cryptography very few asymmetric encryption methods achieve the fast transmission of data).
- Asymmetric key cryptography utilizes more resources as compared to symmetric key cryptography.
